Cybercrime is escalating. Over the past decade, every year has seen a dramatic increase in the number of successful attacks, breaches, and thefts on businesses and individuals alike. While cybersecurity is advancing in its defense tactics, everyone should understand possible threats to their private data. Fortunately, a significant portion of the cyberthreat landscape has remained unchanged for decades — but the new stuff is utterly terrifying. Here are the old and new threats facing everyone in 2018.
The Old
Old cyberattack techniques are so familiar to most tech users that they have become running jokes. Most TV shows contain at least one goof about online advertisements for dubious health products or emails from African princes asking for money. However, as laughably easy to spot as these tactics might seem, in truth they negatively affect millions of people every year. Thus, it remains important to stay vigilant for the following “old” cyberthreats:
- Phishing. Phishing is the sending fraudulent messages that purport to be from an individual or institution and request recipients’ information or money, and it is a serious (and seriously common) crime. However, long gone are the days of African princes; these days, phishers are armed with legitimate-looking emails from people and companies that recipients actually interact with, so the chance of getting fooled is much higher.
- Spam. Spam is the indiscriminate spread of messages over the internet in the attempt to reach recipients who might otherwise ignore those messages. Unfortunately, most spam is more than annoying — it’s dangerous. Spam often contains corrupt links that download malware or steal data; thankfully, the best internet security suites are proficient at blocking most spam.
The Familiar
Phishing and spam have been around since computers and the internet first emerged as dominant technologies, but sometime between the advent of cybercrime and last year, other serious threats have developed. Though the following cyber-concerns aren’t exactly brand new, they are worth guarding against in the coming years:
- Data breaches. Every year brings more and more high-profile data breaches, and it is beginning to seem like no organization is safe. In truth, most data breaches can be traced back to human error, so businesses (and individuals!) who don’t want to lose data should become educated and experienced with cyber hygiene.
- Social engineering. Social engineering is the manipulation of human behavior — and in infosec, the application of social engineering is usually for criminal gain. Often, social engineering is applied in conjunction with another tactic, like phishing. For example, after Experian’s data breach, cybercriminals sent out emails with information about the breach, asking recipients to download fake security software (which was actually malware) or share sensitive information like social security numbers and payment accounts.
- Ransomware. The scariest malware of the 2010s is beginning to diminish in popularity, but ransomware can still easily be found around the web. This malware hijacks control of devices and demands payment of some type — sometimes in personal information, sometimes in cryptocurrency — to return hidden or encrypted data. Though incredibly effective and difficult to combat, ransomware is based on old-fashioned malware techniques, and many cybercriminals are looking for faster and more efficient ways to generate money and data.
- Botnets. A botnet is a network of devices whose control has been taken over without their owners’ knowledge or consent. Cybercriminals use botnets to launch massive attacks on otherwise strong and sturdy cyber-defenses. Recently, botnets have been fashioned from vulnerable Internet of Things devices to bring down major institutions — and the entire internet could be next.
The New
Because these threats are relatively new, security experts can’t say for certain how they will impact cybersecurity, devices, and users. Still, stories surrounding the following cybercrime techniques are sure to appear in the news in coming years, so it is best to be abreast of them:
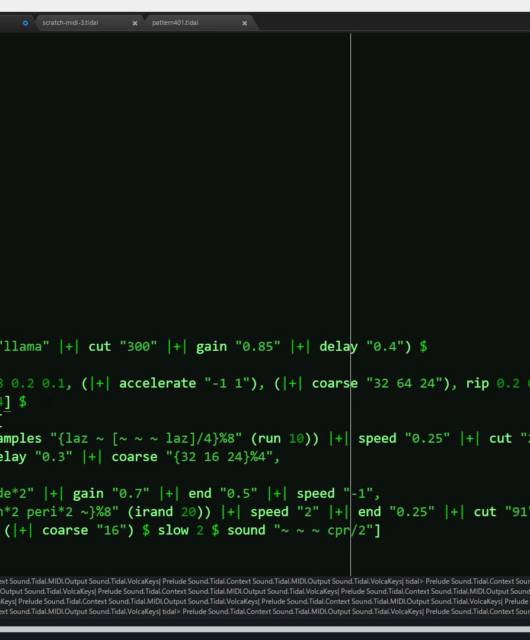
- Cryptocurrency mining. Given that cryptocurrencies are proving to be incredibly lucrative investments, many people are trying to get their hands on a digital coin or to by any means necessary. Cryptocurrency mining is the act of generating cryptocurrency by computing complex equations, but the process is incredibly taxing on hardware. Thus, cybercriminals spread mining malware that runs in the background of unsuspecting users’ computers, allowing them to avoid the costs of cryptocurrency while enjoying the spoils.
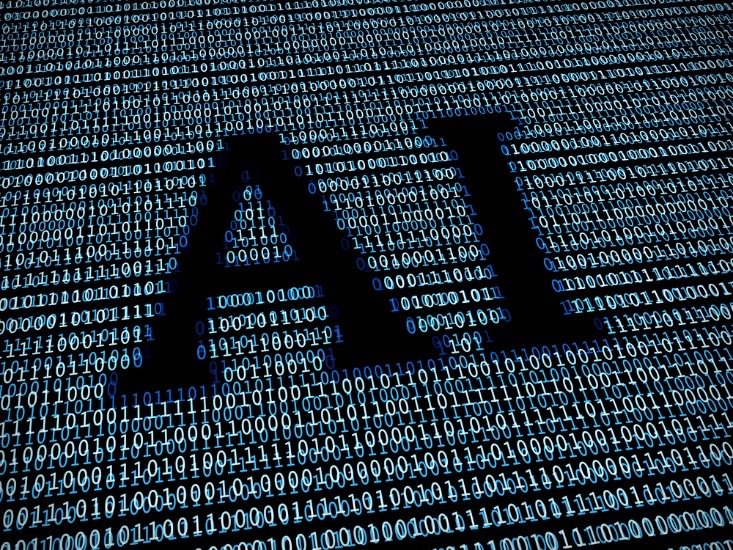
- Weaponizing AI. The problem with computer programs has long been their inability to adapt to new information and situations — until now. Artificial intelligence allows software to gather information and develop optimal techniques without developer interference. Unfortunately, cybercriminals are using AI to create unstoppable, learning malware.